Wells - WiFi Hacking for Beginners: Learn Hacking by Hacking WiFi networks (Penetration testing, Hacking, Wireless Networks)
Here you can read online Wells - WiFi Hacking for Beginners: Learn Hacking by Hacking WiFi networks (Penetration testing, Hacking, Wireless Networks) full text of the book (entire story) in english for free. Download pdf and epub, get meaning, cover and reviews about this ebook. year: 2017, genre: Romance novel. Description of the work, (preface) as well as reviews are available. Best literature library LitArk.com created for fans of good reading and offers a wide selection of genres:
Romance novel
Science fiction
Adventure
Detective
Science
History
Home and family
Prose
Art
Politics
Computer
Non-fiction
Religion
Business
Children
Humor
Choose a favorite category and find really read worthwhile books. Enjoy immersion in the world of imagination, feel the emotions of the characters or learn something new for yourself, make an fascinating discovery.
- Book:WiFi Hacking for Beginners: Learn Hacking by Hacking WiFi networks (Penetration testing, Hacking, Wireless Networks)
- Author:
- Genre:
- Year:2017
- Rating:4 / 5
- Favourites:Add to favourites
- Your mark:
- 80
- 1
- 2
- 3
- 4
- 5
WiFi Hacking for Beginners: Learn Hacking by Hacking WiFi networks (Penetration testing, Hacking, Wireless Networks): summary, description and annotation
We offer to read an annotation, description, summary or preface (depends on what the author of the book "WiFi Hacking for Beginners: Learn Hacking by Hacking WiFi networks (Penetration testing, Hacking, Wireless Networks)" wrote himself). If you haven't found the necessary information about the book — write in the comments, we will try to find it.
WiFi Hacking for Beginners: Learn Hacking by Hacking WiFi networks (Penetration testing, Hacking, Wireless Networks) — read online for free the complete book (whole text) full work
Below is the text of the book, divided by pages. System saving the place of the last page read, allows you to conveniently read the book "WiFi Hacking for Beginners: Learn Hacking by Hacking WiFi networks (Penetration testing, Hacking, Wireless Networks)" online for free, without having to search again every time where you left off. Put a bookmark, and you can go to the page where you finished reading at any time.
Font size:
Interval:
Bookmark:
James Wells
Copyright by James Wells. Distribution of this book in any form or in any way (mechanical, electronic...), or usage of material(s) from the book is prohibited without written permission from the author.
Table of Contents
In this chapter, you will learn how to set up the lab for hacking. So, you may have operation system like Windows, Linux or Mac OS X but for hacking you need specified operation system like Kali or Backtrack. These operation systems are created for hacking and penetration testing. They have support almost all of hacking programs. Good news, these operation systems are free. In this book, we are going to install and use Kali. These both operation systems are Linux but there are few differences. When we install Kali, there will be preinstalled programs that can be used for hacking. Maybe you think there is a problem that you must install new operation system on your computer, but there are some programs that help you virtualize operation systems. There are two famous programs called VirtualBox and VMware Workstation. We are going to use VirtualBox because it is free and it has almost same functions. VirtualBox is a free and open-source program that lets you virtualize operation systems like Windows, Linux, Mac OS X and even your own operation systems. It supports almost all operation system. So, you dont even need to install Kali on your computer you can simply install Kali in VirtualBox and then use it as common computer. First of all, download VirtualBox latest version and install it. Here is a link available:
https://www.virtualbox.org/wiki/Downloads
if you are using windows operation system you should download for windows hosts binary release, if you are using Linux download for Linux operation system and if you are using Mac OS X download for it. We also need something called Virtualbox Extention Pack(you can find and download it from virtualbox download link), which lets us input USBs, wireless adapters and many portable devices. First install VirtualBox and then double-click extention pack and click install, installation is very easy, so I am not going to explain it. Once you have installed it, we need a Kali operation system to install on VirtualBox. But why lose time when you can simply download already installed Kali? In the Kali website, there is link to download Kali virtual images, then you can just open these virtual images on VirtualBox and start Kali. There are for VMware Workstation and for VirtualBox and you must download for VirtualBox no matter what operation system you have. Once you have finished downloading, go to the Downloads folder and search Kali virtual image, the extension must be ova, then double-click it and wait before process ends. If the image has sucessfully installed, look for settings button and click it. So first of all, go to the system and correctly enter ram usage for virtual machine (remember, your operation system needs at least two gb of ram), then you gonna go to the system>processor and enter usage of processor, also very important is to set up network connection, because without that you will not able to do something with Kali. To do this, go to the network and choose Bridged Adapter this means that program will use your built-in wireless adapter. Now you are ready to start virtual machine. Click Start and wait before username promt appears. the default username is root, and default password is toor, but for security we going to change it later. The screen should look like this:
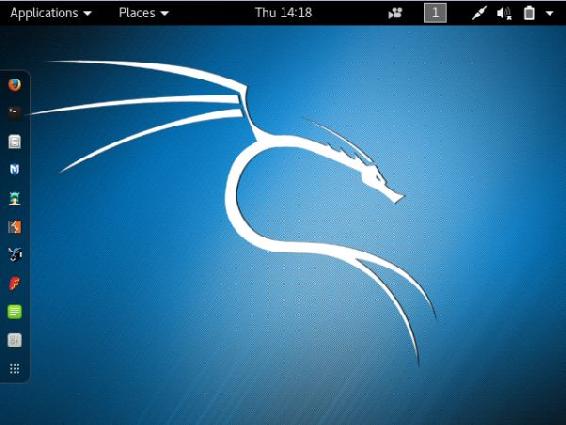
On the left side should be program called terminal, click on it and you will see that black screen appears with red promt root@kali#. You may have question like what does root means?, well root is an access type, to understand easly this is access when you have full access over computer, you can do anything what your computer is able to do. In windows you may think that Administrator is a highest level access but that is not so. Highest level access is root. This is where we going to run our commands. From terminal, you can run programs easly and do whatever you want. Our system is may out of date, so run command apt-get update to update system and wait until promt appears. The apt-get is a program that lets us to update system and install programs easly (we will use it often later), so with the command apt-get update we are calling the apt-get program and telling it to update system. Once you have updated system we need to change password because it is default, and anyone can access to it. To change password open again terminal and run command passwd, then it going to ask you old password, enter toorand click enter, and enter new password (does not metter what it will be) and remember it. So to power off virtual machine correctly click on the button to the up and right and then click on the power off sign. Now we already set up everything, and ready to learn how to hide your identify how to become untraceable.
In hacking very important thing it to be untraceable. To be able to hack something is nothing without hiding your identify. For example, imagine that you hacked someones wifi and did not hide identify, in few days police will analysis wifi router and there will be your computer information and finally they will find you and throw into prison. So very important part of entire hacking to hide identify and make hack untraceable. In this chapter you going to learn about how to be anonymous, hide identify and how to become fully untraceable.
What is mac address?
A MAC address (media access control address) is a unique identifier assigned to network interfaces for communications on the physical network segment. Every computer device have different MAC address. The MAC address is a built-in every computer device when it is created. When computer starts, operation system reads from hardware device. When you are connected to the wireless network, it sends packets to you and then your computer converts these information to websites, movies, images Imagine that two computers are connected to the wireless network, first computer wants website google.com, and the second computer wants amazon.com, network sends packets to these computers, but how do these computers know what packets ignore and what packets to recive? Computers identify packets to recive or ignore by MAC address, when the network is sending packet to computer, it also writes in packet the MAC address of the computer it is sending. that is the way how wireless networks and computers are connecting each other. So, if you do not change your ip and hack someones wireless network, you let them to investigate your identify by analysing network history.
How to hide MAC address?
You may think that how you can change MAC address if computer reads it from hardware? You are not going to make modification on hardware, you going to change RAM. When the computer starts, MAC address loads in RAM and we going to change already loaded MAC address.. So, when you change your MAC address police will find your fake MAC address and they will not be able to trace hacker. Now you have basic information about what is MAC address, dangers of hacking without changing MAC address, how police can trace you, how we can change it.
Change MAC address by Kali
Kali has already installed program called macchanger which lets us to changeloaded MAC address in RAM. Open VirtualBox, start kali virtual machine and open terminal. We need to stop our wireless card to change the MAC address. Type in ifconfig wlan0 down. The ifconfig is a program, wlan0 is our wireless card and the down is action what we want to do. So, this command will stop every wireless service and it is nessesary to stop network card before changing the MAC address. Then type in the following command macchanger --help.This command tells Kali to call macchanger and show help. There is program usage instructions. In my case, I will use random MAC address by entering macchanger random wlan0.macchanger is program name random is an option and wlan0 is wireless card. If everything is correct the screen should look like this:
Font size:
Interval:
Bookmark:
Similar books «WiFi Hacking for Beginners: Learn Hacking by Hacking WiFi networks (Penetration testing, Hacking, Wireless Networks)»
Look at similar books to WiFi Hacking for Beginners: Learn Hacking by Hacking WiFi networks (Penetration testing, Hacking, Wireless Networks). We have selected literature similar in name and meaning in the hope of providing readers with more options to find new, interesting, not yet read works.
Discussion, reviews of the book WiFi Hacking for Beginners: Learn Hacking by Hacking WiFi networks (Penetration testing, Hacking, Wireless Networks) and just readers' own opinions. Leave your comments, write what you think about the work, its meaning or the main characters. Specify what exactly you liked and what you didn't like, and why you think so.