316_Buff_Oflow_FM.qxd 12/28/04 5:44 PM Page i
Register for Free Membership to
s o l u t i o n s @ s y n g r e s s . c o m
Over the last few years, Syngress has published many best
selling and critically acclaimed books, including Tom Shinders
Configuring ISA Server 2000, Brian Caswell and Jay Beales
Snort 2.0 Intrusion Detection, and Angela Orebaugh and
Gilbert Ramirezs Ethereal Packet Sniffing. One of the
reasons for the success of these books has been our unique
solutions@syngress.com program. Through this site, weve
been able to provide readers a real time extension to the
printed book.
As a registered owner of this book, you will qualify for free
access to our members-only solutions@syngress.com
program. Once you have registered, you will enjoy several
benefits, including:
Four downloadable e-booklets on topics related to the
book. Each booklet is approximately 20-30 pages in Adobe
PDF format. They have been selected by our editors from
other best-selling Syngress books as providing topic cov
erage that is directly related to the coverage in this book.
A comprehensive FAQ page that consolidates all of the key
points of this book into an easy to search web page, pro
viding you with the concise, easy to access data you need
to perform your job.
A From the Author Forum that allows the authors of this
book to post timely updates links to related sites, or addi
tional topic coverage that may have been requested by
readers.
Just visit us at www.syngress.com/solutions and follow the
simple registration process. You will need to have this book
with you when you register.
Thank you for giving us the opportunity to serve your needs.
And be sure to let us know if there is anything else we can
do to make your job easier.

316_Buff_Oflow_FM.qxd 12/28/04 5:44 PM Page ii
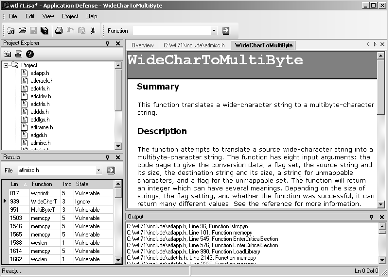
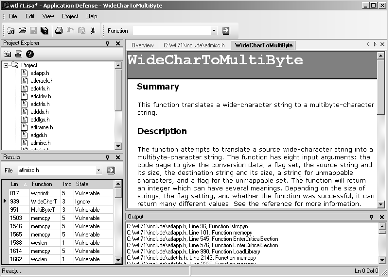
Application Defense
www.applicationdefense.com
Application Defense Specials
Free Software with Purchase of Application Security Services
Program
$1,000 Enterprise Language Special Until February 2005
with Proof of Purchase of Ultimate DeskRef.
Business Benefits
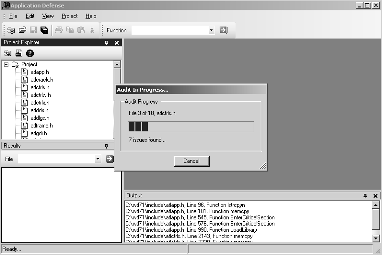
Application Defense Developer Edition, strives to educate
individual developers on proper secure programming tech
niques during the development cycle, thereby saving thou
sands in post-development consulting
Developmental education approach on secure development
strengthens your business at the core, its people
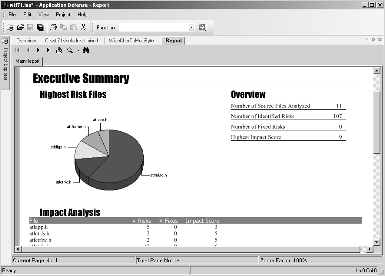
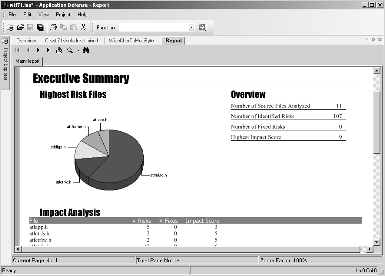
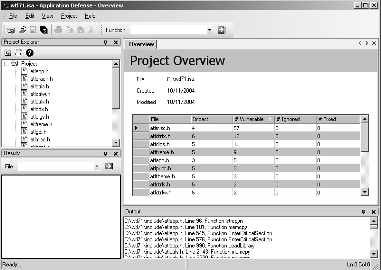
Executive-level reporting allows your development team to
visually depict trending improvements, vulnerability remedia
tion, and high-risk segments of code
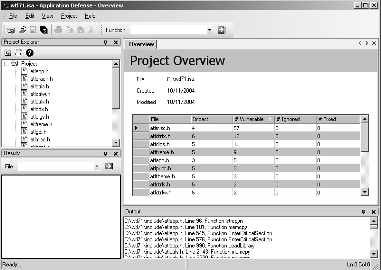
Distributed Software Architecture permits development teams
to review their code centrally by a QA or Auditing team or
individually by the developers
Industry-best multi-language support permits organizations to
manage all their software development needs with one appli
cation
Application Defense Technology Features:
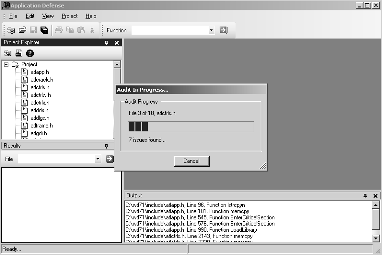
Industry leading analysis engine can parse and examine
entire software code base in under a minute
Executive, technical, and trending reports allow information
to be displayed for all audiences
Flexible XML output allows easy integration with other
enterprise applications
Unique IDE allows you to update results in real-time or in
batches to code base no need to recreate code in multiple
locations!
Custom developer code is analyzed by proprietary artificial
intelligence engine
Project file storage allows developers to save analysis results
for later review or to save for continued analysis
Real-time bug tracking system
Interactive software interface allows developers to make
security decisions during analysis
Able to input Visual Studio Project files
Customizable reports allow you to specify company name,
application, auditor, and more

316_Buff_Oflow_FM.qxd 12/28/04 5:45 PM Page iii
Buffer
Overflow
Attacks
D E T E C T, E X P L O I T, P R E V E N T
James C. Foster
Vitaly Osipov
FOREWORD
Nish Bhalla
BY DAVE AITEL
FOUNDER AND CEO
Niels Heinen
IMMUNITY, INC.
316_Buff_Oflow_FM.qxd 12/28/04 5:45 PM Page iv
Syngress Publishing, Inc., the author(s), and any person or firm involved in the writing, editing, or production (collectively Makers) of this book (the Work) do not guarantee or warrant the results to be obtained from the Work.
There is no guarantee of any kind, expressed or implied, regarding the Work or its contents.The Work is sold AS IS and WITHOUT WARRANTY.You may have other legal rights, which vary from state to state.
In no event will Makers be liable to you for damages, including any loss of profits, lost savings, or other incidental or consequential damages arising out from the Work or its contents. Because some states do not allow the exclusion or limitation of liability for consequential or incidental damages, the above limitation may not apply to you.
You should always use reasonable care, including backup and other appropriate precautions, when working with computers, networks, data, and files.
Syngress Media, Syngress, Career Advancement Through Skill Enhancement, Ask the Author UPDATE, and Hack Proofing, are registered trademarks of Syngress Publishing, Inc. Syngress:The Definition of a Serious Security Library, Mission Critical, and The Only Way to Stop a Hacker is to Think Like One are trademarks of Syngress Publishing, Inc. Brands and product names mentioned in this book are trademarks or service marks of their respective companies.
KEY
SERIAL NUMBER
HJIRTCV764
PO9873D5FG
829KM8NJH2
HJBC43288N
CVPLQ6WQ23
VBP965T5T5
HJJJ863WD3E
2987GVTWMK
629MP5SDJT
IMWQ295T6T
PUBLISHED BY
Syngress Publishing, Inc.
800 Hingham Street
Rockland, MA 02370
Buffer Overflow Attacks: Detect, Exploit, Prevent
Copyright 2005 by Syngress Publishing, Inc. All rights reserved. Printed in the United States of America. Except as permitted under the Copyright Act of 1976, no part of this publication may be reproduced or distributed in any form or by any means, or stored in a database or retrieval system, without the prior written permission of the publisher, with the exception that the program listings may be entered, stored, and executed in a computer system, but they may not be reproduced for publication.
Next page