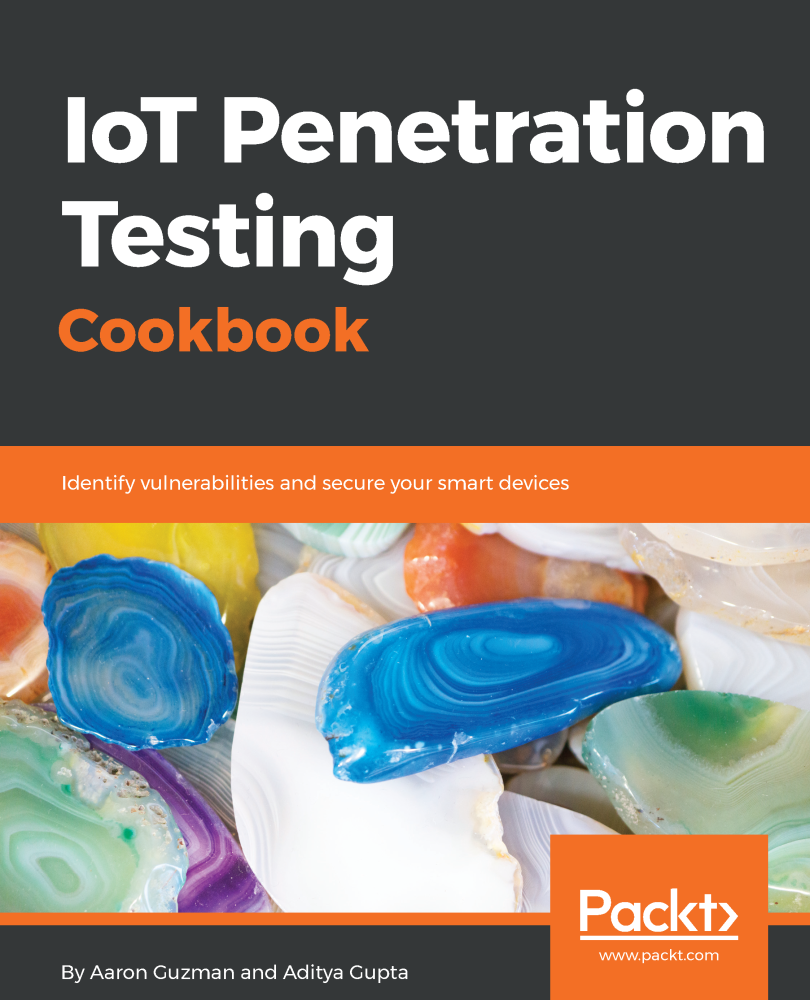
Guzman Aaron - IoT penetration testing cookbook: identify vulnerabilities and secure your smart devices
Here you can read online Guzman Aaron - IoT penetration testing cookbook: identify vulnerabilities and secure your smart devices full text of the book (entire story) in english for free. Download pdf and epub, get meaning, cover and reviews about this ebook. City: Birmingham Packt November, year: 2017, publisher: Packt Publishing Limited, genre: Computer. Description of the work, (preface) as well as reviews are available. Best literature library LitArk.com created for fans of good reading and offers a wide selection of genres:
Romance novel
Science fiction
Adventure
Detective
Science
History
Home and family
Prose
Art
Politics
Computer
Non-fiction
Religion
Business
Children
Humor
Choose a favorite category and find really read worthwhile books. Enjoy immersion in the world of imagination, feel the emotions of the characters or learn something new for yourself, make an fascinating discovery.

- Book:IoT penetration testing cookbook: identify vulnerabilities and secure your smart devices
- Author:
- Publisher:Packt Publishing Limited
- Genre:
- Year:2017
- City:Birmingham Packt November
- Rating:5 / 5
- Favourites:Add to favourites
- Your mark:
IoT penetration testing cookbook: identify vulnerabilities and secure your smart devices: summary, description and annotation
We offer to read an annotation, description, summary or preface (depends on what the author of the book "IoT penetration testing cookbook: identify vulnerabilities and secure your smart devices" wrote himself). If you haven't found the necessary information about the book — write in the comments, we will try to find it.
Over 80 recipes to master IoT security techniques.
About This Book
- Identify vulnerabilities in IoT device architectures and firmware using software and hardware pentesting techniques
- Understand radio communication analysis with concepts such as sniffing the air and capturing radio signals
- A recipe based guide that will teach you to pentest new and unique set of IoT devices.
Who This Book Is For
This book targets IoT developers, IoT enthusiasts, pentesters, and security professionals who are interested in learning about IoT security. Prior knowledge of basic pentesting would be beneficial.
What You Will Learn
- Set up an IoT pentesting lab
- Explore various threat modeling concepts
- Exhibit the ability to analyze and exploit firmware vulnerabilities
- Demonstrate the automation of application binary analysis for iOS and Android using MobSF
- Set up a Burp Suite and use it for web app testing
- Identify UART and JTAG pinouts, solder headers, and hardware debugging
- Get solutions to common wireless protocols
- Explore the mobile security and firmware best practices
- Master various advanced IoT exploitation techniques and security automation
In Detail
IoT is an upcoming trend in the IT industry today; there are a lot of IoT devices on the market, but there is a minimal understanding of how to safeguard them. If you are a security enthusiast or pentester, this book will help you understand how to exploit and secure IoT devices.
This book follows a recipe-based approach, giving you practical experience in securing upcoming smart devices. It starts with practical recipes on how to analyze IoT device architectures and identify vulnerabilities. Then, it focuses on enhancing your pentesting skill set, teaching you how to exploit a vulnerable IoT device, along with identifying vulnerabilities in IoT device firmware. Next, this book teaches you how to secure embedded devices and exploit smart devices with hardware techniques. Moving forward, this book reveals advanced hardware pentesting techniques, along with software-defined, radio-based IoT pentesting with Zigbee and Z-Wave. Finally, this book also covers how to use new and unique pentesting techniques for different IoT devices, along with smart devices connected to the cloud.
By the end of this book, you will have a fair understanding of how to use different pentesting techniques to exploit and secure various IoT devices.
Style and approach
This recipe-based book will teach you how to use advanced IoT exploitation and security automation.
Downloading the example code for this book. You can download the example code files for all Packt books you have purchased from your account at http://www.PacktPub.com. If you purchased this book elsewhere, you can visit http://www.PacktPub.com/support and register to have the code file.
Guzman Aaron: author's other books
Who wrote IoT penetration testing cookbook: identify vulnerabilities and secure your smart devices? Find out the surname, the name of the author of the book and a list of all author's works by series.