Yan Lin - Novel Techniques in Recovering, Embedding, and Enforcing Policies for Control-Flow Integrity (Information Security and Cryptography)
Here you can read online Yan Lin - Novel Techniques in Recovering, Embedding, and Enforcing Policies for Control-Flow Integrity (Information Security and Cryptography) full text of the book (entire story) in english for free. Download pdf and epub, get meaning, cover and reviews about this ebook. year: 2021, publisher: Springer, genre: Computer. Description of the work, (preface) as well as reviews are available. Best literature library LitArk.com created for fans of good reading and offers a wide selection of genres:
Romance novel
Science fiction
Adventure
Detective
Science
History
Home and family
Prose
Art
Politics
Computer
Non-fiction
Religion
Business
Children
Humor
Choose a favorite category and find really read worthwhile books. Enjoy immersion in the world of imagination, feel the emotions of the characters or learn something new for yourself, make an fascinating discovery.
Novel Techniques in Recovering, Embedding, and Enforcing Policies for Control-Flow Integrity (Information Security and Cryptography): summary, description and annotation
We offer to read an annotation, description, summary or preface (depends on what the author of the book "Novel Techniques in Recovering, Embedding, and Enforcing Policies for Control-Flow Integrity (Information Security and Cryptography)" wrote himself). If you haven't found the necessary information about the book — write in the comments, we will try to find it.
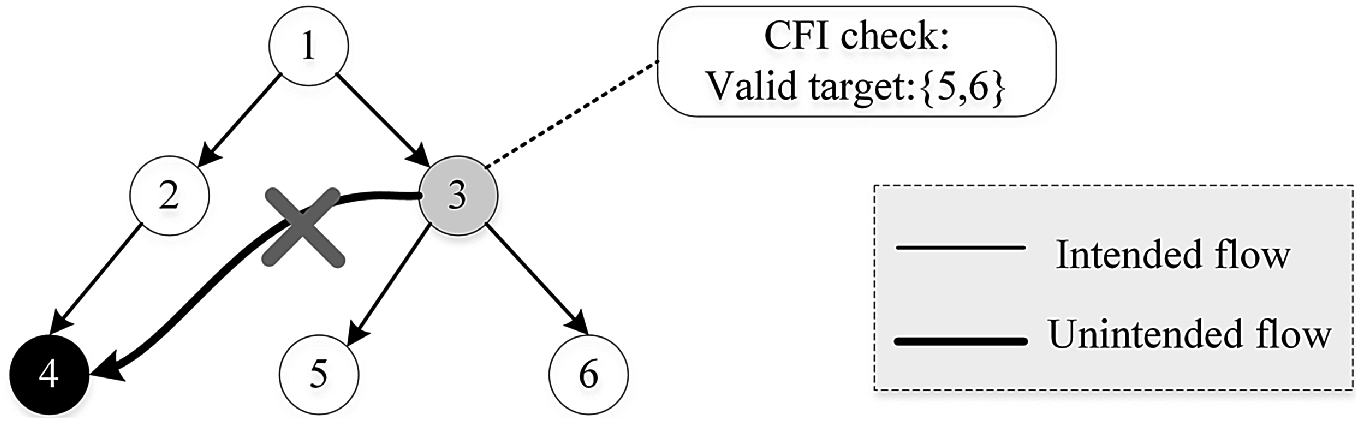
In this book, we propose novel solutions to handle these three fundamental components. To generate a precise CFI policy without the support of the source code, we systematically study two methods which recover CFI policy based on function signature matching at the binary level and propose our novel rule- and heuristic-based mechanism to more accurately recover function signature. To embed CFI policy securely, we design a novel platform which encodes the policy into the machine instructions directly without relying on consulting any read-only data structure, by making use of the idea of instruction-set randomization. Each basic block is encrypted with a key derived from the CFG. To efficiently enforce CFI policy, we make use of a mature dynamic code optimization platform called DynamoRIO to enforce the policy so that we are only required to do the CFI check when needed.
Yan Lin: author's other books
Who wrote Novel Techniques in Recovering, Embedding, and Enforcing Policies for Control-Flow Integrity (Information Security and Cryptography)? Find out the surname, the name of the author of the book and a list of all author's works by series.