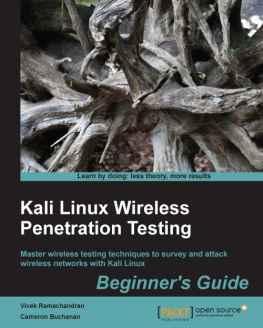
Cameron Buchanan - Kali Linux Wireless Penetration Testing Beginners Guide -Third
Here you can read online Cameron Buchanan - Kali Linux Wireless Penetration Testing Beginners Guide -Third full text of the book (entire story) in english for free. Download pdf and epub, get meaning, cover and reviews about this ebook. City: Birmingham, year: 2019, publisher: Packt Publishing, Limited, genre: Home and family. Description of the work, (preface) as well as reviews are available. Best literature library LitArk.com created for fans of good reading and offers a wide selection of genres:
Romance novel
Science fiction
Adventure
Detective
Science
History
Home and family
Prose
Art
Politics
Computer
Non-fiction
Religion
Business
Children
Humor
Choose a favorite category and find really read worthwhile books. Enjoy immersion in the world of imagination, feel the emotions of the characters or learn something new for yourself, make an fascinating discovery.
- Book:Kali Linux Wireless Penetration Testing Beginners Guide -Third
- Author:
- Publisher:Packt Publishing, Limited
- Genre:
- Year:2019
- City:Birmingham
- Rating:4 / 5
- Favourites:Add to favourites
- Your mark:
- 80
- 1
- 2
- 3
- 4
- 5
Kali Linux Wireless Penetration Testing Beginners Guide -Third: summary, description and annotation
We offer to read an annotation, description, summary or preface (depends on what the author of the book "Kali Linux Wireless Penetration Testing Beginners Guide -Third" wrote himself). If you haven't found the necessary information about the book — write in the comments, we will try to find it.
Kali Linux Wireless Penetration Testing Beginners Guide -Third — read online for free the complete book (whole text) full work
Below is the text of the book, divided by pages. System saving the place of the last page read, allows you to conveniently read the book "Kali Linux Wireless Penetration Testing Beginners Guide -Third" online for free, without having to search again every time where you left off. Put a bookmark, and you can go to the page where you finished reading at any time.
Font size:
Interval:
Bookmark:
Copyright 2017 Packt Publishing
All rights reserved. No part of this book may be reproduced, stored in a retrieval system, or transmitted in any form or by any means, without the prior written permission of the publisher, except in the case of brief quotations embedded in critical articles or reviews.
Every effort has been made in the preparation of this book to ensure the accuracy of the information presented. However, the information contained in this book is sold without warranty, either express or implied. Neither the authors, nor Packt Publishing, and its dealers and distributors will be held liable for any damages caused or alleged to be caused directly or indirectly by this book.
Packt Publishing has endeavored to provide trademark information about all of the companies and products mentioned in this book by the appropriate use of capitals. However, Packt Publishing cannot guarantee the accuracy of this information.
First published: September 2011
Second edition: March 2015
Third edition: December 2017
Production reference: 1261217
Published by Packt Publishing Ltd.
Livery Place
35 Livery Street
Birmingham B3 2PB, UK.
ISBN 978-1-78883-192-5
www.packtpub.com
Authors
Cameron Buchanan
Vivek Ramachandran
Reviewer
Daniel W. Dieterle
Acquisition Editor
Ben Renow-Clarke
Project Editor
Suzanne Coutinho
Technical Editor
Bhagyashree Rai
Proofreader
Safis Editing
Indexer
Rekha Nair
Graphics
Tom Scaria
Production Coordinator
Arvindkumar Gupta
The content within this book is for educational purposes only. It is designed to help users test their own system against information security threats and protect their IT infrastructure from similar attacks. Packt Publishing and the authors of this book take no responsibility for actions resulting from the inappropriate usage of learning material contained within this book.
Cameron Buchanan is a penetration tester by trade and a writer in his spare time. He has performed penetration tests around the world for a variety of clients across many industries. Previously, Cameron was a member of the RAF. In his spare time, he enjoys doing stupid things, such as trying to make things fly, getting electrocuted, and dunking himself in freezing cold water. He is married and lives in London.
Vivek Ramachandran has been working on Wi-Fi security since 2003. He discovered the Caffe Latte attack and also broke WEP Cloaking, a WEP protection schema, publicly in 2007 at DEF CON. In 2011, he was the first to demonstrate how malware could use Wi-Fi to create backdoors, worms, and even botnets.
Earlier, Vivek was one of the programmers of the 802.1x protocol and Port Security in Cisco's 6500 Catalyst series of switches, and he was also one of the winners of the Microsoft Security Shootout contest held in India among a reported 65,000 participants. He is best known in the hacker community as the founder of SecurityTube.net, where he routinely posts videos on Wi-Fi security, assembly language, exploitation techniques, and so on. SecurityTube.net receives over 100,000 unique visitors a month.
Vivek's work on wireless security has been quoted in BBC Online, InfoWorld, MacWorld, The Register, IT World Canada, and so on. This year, he will speak or train at a number of security conferences, including Blackhat, DEF CON, Hacktivity, 44con, HITB-ML, BruCON Derbycon, Hashdays, SecurityZone, and SecurityByte.
Daniel W. Dieterle is an internationally published security author, researcher, and technical editor. He has over 20 years of IT experience and has provided various levels of support and service to hundreds of companies, ranging from small businesses to large corporations. Daniel authors and runs the Cyber Arms - Security Blog (https://cyberarms.wordpress.com/) and an Internet of Things projects and security-based blog (https://dantheiotman.com/).
Did you know that Packt offers eBook versions of every book published, with PDF and ePub files available? You can upgrade to the eBook version at > for more details.
At www.PacktPub.com, you can also read a collection of free technical articles, sign up for a range of free newsletters and receive exclusive discounts and offers on Packt books and eBooks.

https://www.packtpub.com/mapt
Get the most in-demand software skills with Mapt. Mapt gives you full access to all Packt books and video courses, as well as industry-leading tools to help you plan your personal development and advance your career.
- Fully searchable across every book published by Packt
- Copy and paste, print, and bookmark content
- On demand and accessible via a web browser
Thanks for purchasing this Packt book. At Packt, quality is at the heart of our editorial process. To help us improve, please leave us an honest review on this book's Amazon page at https://www.amazon.com/dp/1788831926.
If you'd like to join our team of regular reviewers, you can email us at <>. We award our regular reviewers with free eBooks and videos in exchange for their valuable feedback. Help us be relentless in improving our products!
Wireless networks have become ubiquitous in today's world. Millions of people use it worldwide every day at their homes, offices, and public hotspots to log on to the internet and do both personal and professional work. Even though wireless makes life incredibly easy and gives us such great mobility, it comes with its risks. In recent times, insecure wireless networks have been used to break into companies, banks, and government organizations. The frequency of these attacks is only intensified, as network administrators are still clueless on how to secure wireless networks in a robust and fool proof way.
Kali Linux Wireless Penetration Testing Beginner's Guide , Third Edition , is aimed at helping the reader understand the insecurities associated with wireless networks, and how to conduct penetration tests to find and plug them. This is an essential read for those who would like to conduct security audits on wireless networks and always wanted a step-by-step practical guide for this. With this book, your learning will be complete, as every wireless attack explained is immediately followed by a practical demo.
We have chosen Kali Linux as the platform to test all the wireless attacks in this book. Kali Linux, as you might already be aware, is the world's most popular penetration testing distribution. It contains hundreds of security and hacking tools, some of which we will use in this book.
, Wireless Lab Setup , shows how to create a wireless testing lab using off-the-shelf hardware and open source software. In order to be able to try out the dozens of exercises in this book, you will need to set up a wireless lab. We will first look at the hardware requirements, which include wireless cards, antennas, access points, and other Wi-Fi enabled devices. Then we will shift our focus to the software requirements, which include the operating system, Wi-Fi drivers, and security tools. Finally, we will create a test bed for our experiments and verify the different wireless configurations on it.
Font size:
Interval:
Bookmark:
Similar books «Kali Linux Wireless Penetration Testing Beginners Guide -Third»
Look at similar books to Kali Linux Wireless Penetration Testing Beginners Guide -Third. We have selected literature similar in name and meaning in the hope of providing readers with more options to find new, interesting, not yet read works.
Discussion, reviews of the book Kali Linux Wireless Penetration Testing Beginners Guide -Third and just readers' own opinions. Leave your comments, write what you think about the work, its meaning or the main characters. Specify what exactly you liked and what you didn't like, and why you think so.