Copyright 2015 by McGraw-Hill Education. All rights reserved. Except as permitted under the United States Copyright Act of 1976, no part of this publication may be reproduced or distributed in any form or by any means, or stored in a database or retrieval system, without the prior written permission of the publisher, with the exception that the program listings may be entered, stored, and executed in a computer system, but they may not be reproduced for publication.
ISBN: 978-0-07-183155-0
MHID: 0-07-183155-X
The material in this eBook also appears in the print version of this title: ISBN: 978-0-07-183156-7, MHID: 0-07-183156-8.
eBook conversion by codeMantra
Version 1.0
All trademarks are trademarks of their respective owners. Rather than put a trademark symbol after every occurrence of a trademarked name, we use names in an editorial fashion only, and to the benefit of the trademark owner, with no intention of infringement of the trademark. Where such designations appear in this book, they have been printed with initial caps.
McGraw-Hill Education eBooks are available at special quantity discounts to use as premiums and sales promotions or for use in corporate training programs. To contact a representative, please visit the Contact Us page at www.mhprofessional.com.
All trademarks or copyrights mentioned herein are the possession of their respective owners and McGraw-Hill Education makes no claim of ownership by the mention of products that contain these marks.
courtesy of ErrantX.
.
courtesy of Viljo Viitanen.
.
Information has been obtained by McGraw-Hill Education from sources believed to be reliable. However, because of the possibility of human or mechanical error by our sources, McGraw-Hill Education, or others, McGraw-Hill Education does not guarantee the accuracy, adequacy, or completeness of any information and is not responsible for any errors or omissions or the results obtained from the use of such information.
TERMS OF USE
This is a copyrighted work and McGraw-Hill Education and its licensors reserve all rights in and to the work. Use of this work is subject to these terms. Except as permitted under the Copyright Act of 1976 and the right to store and retrieve one copy of the work, you may not decompile, disassemble, reverse engineer, reproduce, modify, create derivative works based upon, transmit, distribute, disseminate, sell, publish or sublicense the work or any part of it without McGraw-Hill Educations prior consent. You may use the work for your own noncommercial and personal use; any other use of the work is strictly prohibited. Your right to use the work may be terminated if you fail to comply with these terms.
THE WORK IS PROVIDED AS IS. MCGRAW-HILL EDUCATION AND ITS LICENSORS MAKE NO GUARANTEES OR WARRANTIES AS TO THE ACCURACY, ADEQUACY OR COMPLETENESS OF OR RESULTS TO BE OBTAINED FROM USING THE WORK, INCLUDING ANY INFORMATION THAT CAN BE ACCESSED THROUGH THE WORK VIA HYPERLINK OR OTHERWISE, AND EXPRESSLY DISCLAIM ANY WARRANTY, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO IMPLIED WARRANTIES OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE. McGraw-Hill Education and its licensors do not warrant or guarantee that the functions contained in the work will meet your requirements or that its operation will be uninterrupted or error free. Neither McGraw-Hill Education nor its licensors shall be liable to you or anyone else for any inaccuracy, error or omission, regardless of cause, in the work or for any damages resulting therefrom. McGraw-Hill Education has no responsibility for the content of any information accessed through the work. Under no circumstances shall McGraw-Hill Education and/or its licensors be liable for any indirect, incidental, special, punitive, consequential or similar damages that result from the use of or inability to use the work, even if any of them has been advised of the possibility of such damages. This limitation of liability shall apply to any claim or cause whatsoever whether such claim or cause arises in contract, tort or otherwise.
This book is dedicated to my wife, Helyn Pultz.
ABOUT THE AUTHOR
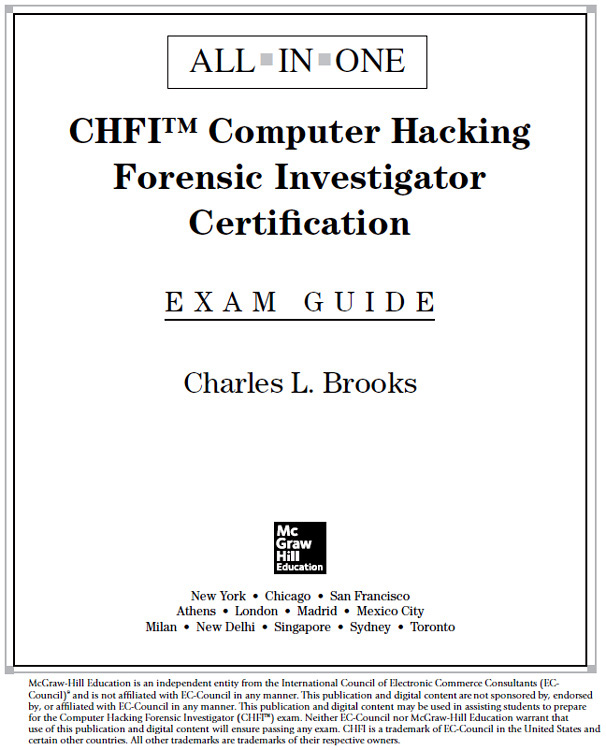
Charles Brooks, MsCIS, CISSP, CEH, CHFI, CTT+, CCNA, CWNA, CWSP, is a writer and educator with a background in IT that spans 30 years, with the last 15 years in information security and education. Since 1998, he has been involved in information security, first as a technical lead for the VPN Advantage IPsec-managed service at Genuity, Inc., and then as overall software architect for the project. At EMC, Charles developed and delivered computer-based and instructor-based training in general information security and storage security. At RSA, Charles developed courses in cloud security fundamentals, network analysis, and advanced analysis and forensics. He has written and contributed to several technical training books, as well as continued to develop graduate-level courses in network security, secure software development, software security testing, and securing virtualized and cloud infrastructures. Charles has taught at several colleges and technical institutes in the Greater Boston area, and currently teaches at Brandeis University in the Rabb School/GPS MSIS program, as well as facilitating online courses at Boston University. Charles is currently the owner/principal consultant at Security Technical Education.
About the Technical Editor
Bobby E. Rogers is an information security engineer working for a major hospital in the southeastern United States. His previous experience includes working as a contractor for Department of Defense agencies, helping to secure, certify, and accredit their information systems. His duties include information system security engineering, risk management, and certification and accreditation efforts. He retired after 21 years in the United States Air Force, serving as a network security engineer and instructor, and has secured networks all over the world. Bobby has a masters degree in information assurance (IA), and is pursuing a doctoral degree in IA from Capitol College, Maryland. His many certifications include CompTIA A+, CompTIA Network+, CompTIA Security+, and CompTIA Mobility+ certifications, as well as CISSP-ISSEP, CEH, and MCSE: Security.
CONTENTS AT A GLANCE
CONTENTS
ACKNOWLEDGMENTS
First of all, thanks to Carole Jelen, my literary agent at Waterside Productions, for putting me in contact with Meghan Manfre, my acquisitions editor at McGraw-Hill Education, and to Meghan for getting this process started and bringing me up to speed. Mary Demery, my acquisitions coordinator, kept me on the straight and narrow and offered guidance and encouragement throughout the project. Thanks as well to Raghavi Khullar, associate project manager at Cenveo Publisher Services, who shepherded this book through copy editing and production, and to Lisa McCoy for copy editing the manuscript and making my tortured prose less so. Im sure that there are others at McGraw-Hill Education who have worked on this book, and I thank them for their contributions as well.
A huge measure of thanks is due to my technical editor, Bobby Rogers. Bobby provided a wealth of constructive criticism and suggestions on how to improve the material, as well as pointing out areas that I needed to clarify and expand. The book is better because of his contributions, and Im a better writer for having worked with him. I wont forget the three-sentences rule!