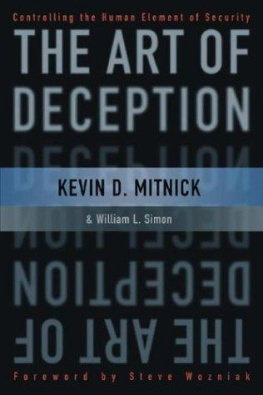
Simon William L. - The art of deception: controlling the human element of security
Here you can read online Simon William L. - The art of deception: controlling the human element of security full text of the book (entire story) in english for free. Download pdf and epub, get meaning, cover and reviews about this ebook. City: Indianapolis;Ind, year: 2002;2011, publisher: John Wiley & Sons, genre: Romance novel. Description of the work, (preface) as well as reviews are available. Best literature library LitArk.com created for fans of good reading and offers a wide selection of genres:
Romance novel
Science fiction
Adventure
Detective
Science
History
Home and family
Prose
Art
Politics
Computer
Non-fiction
Religion
Business
Children
Humor
Choose a favorite category and find really read worthwhile books. Enjoy immersion in the world of imagination, feel the emotions of the characters or learn something new for yourself, make an fascinating discovery.
- Book:The art of deception: controlling the human element of security
- Author:
- Publisher:John Wiley & Sons
- Genre:
- Year:2002;2011
- City:Indianapolis;Ind
- Rating:4 / 5
- Favourites:Add to favourites
- Your mark:
- 80
- 1
- 2
- 3
- 4
- 5
The art of deception: controlling the human element of security: summary, description and annotation
We offer to read an annotation, description, summary or preface (depends on what the author of the book "The art of deception: controlling the human element of security" wrote himself). If you haven't found the necessary information about the book — write in the comments, we will try to find it.
Simon William L.: author's other books
Who wrote The art of deception: controlling the human element of security? Find out the surname, the name of the author of the book and a list of all author's works by series.
The art of deception: controlling the human element of security — read online for free the complete book (whole text) full work
Below is the text of the book, divided by pages. System saving the place of the last page read, allows you to conveniently read the book "The art of deception: controlling the human element of security" online for free, without having to search again every time where you left off. Put a bookmark, and you can go to the page where you finished reading at any time.
Font size:
Interval:
Bookmark:
Publisher: Robert Ipsen Editor: Carol Long
Developmental Editor: Nancy Stevenson
Managing Editor: John Atkins
Interior Design: Marie Kristine Parial-Leonardo
Text Design & Composition: Wiley Composition Services
Chart Design: Stacey Kirkland
Designations used by companies to distinguish their products are often claimed as trademarks. In all instances where Wiley Publishing, Inc., is aware of a claim, the product names appear in initial capital or ALL CAPITAL LETTERS. Readers, however, should contact the appropriate companies for more complete information regarding trademarks and registration.
This book is printed on acid-free paper. 
Copyright 2002 by Kevin D. Mitnick. All rights reserved.
Published by Wiley Publishing, Inc., Indianapolis, Indiana Published simultaneously in Canada
No part of this publication may be reproduced, stored in a retrieval system, or transmitted in any form or by any means, electronic, mechanical, photocopying, recording, scanning, or otherwise, except as permitted under Section 107 or 108 of the 1976 United States Copyright Act, without either the prior written permission of the Publisher, or authorization through payment of the appropriate per-copy fee to the Copyright Clearance Center, Inc., 222 Rosewood Drive, Danvers, MA 01923, (978) 750-8400, fax (978) 750-4470. Requests to the Publisher for permission should be addressed to the Legal Department, Wiley Publishing, Inc., 10475 Crosspoint Blvd., Indianapolis, IN 46256, (317) 572-3447, fax (317) 572-4447, Email: .
Limit of Liability/Disclaimer of Warranty: While the publisher and author have used their best efforts in preparing this book, they make no representations or warranties with respect to the accuracy or completeness of the contents of this book and specifically disclaim any implied warranties of merchantability or fitness for a particular purpose. No warranty may be created or extended by sales representatives or written sales materials. The advice and strategies contained herein may not be suitable for your situation. You should consult with a professional where appropriate. Neither the publisher nor author shall be liable for any loss of profit or any other commercial damages, including but not limited to special, incidental, consequential, or other damages.
For general information on our other products and services please contact our Customer Care Department within the United States at (800) 762-2974, outside the United States at (317) 572-3993 or fax (317) 572-4002.
Wiley also publishes its books in a variety of electronic formats. Some content that appears in print may not be available in electronic books.
ISBN: 0-471-23712-4
For Reba Vartanian, Shelly Jaffe, Chickie Leventhal, and Mitchell Mitnick, and for the late Alan Mitnick, Adam Mitnick, and Jack Biello
For Arynne, Victoria, and David, Sheldon, Vincent, and Elena
Social Engineering
Social engineering uses influence and persuasion to deceive people by convincing them that the social engineer is someone he is not, or by manipulation. As a result, the social engineer is able to take advantage of people to obtain information with or without the use of technology.
Foreword
We humans are born with an inner drive to explore the nature of our surroundings. As young men, both Kevin Mitnick and I were intensely curious about the world and eager to prove ourselves. We were rewarded often in our attempts to learn new things, solve puzzles, and win at games. But at the same time, the world around us taught us rules of behavior that constrained our inner urge toward free exploration. For our boldest scientists and technological entrepreneurs, as well as for people like Kevin Mitnick, following this inner urge offers the greatest thrills, letting us accomplish things that others believe cannot be done.
Kevin Mitnick is one of the finest people I know. Ask him, and he will say forthrightly that what he used to dosocial engineeringinvolves conning people. But Kevin is no longer a social engineer. And even when he was, his motive never was to enrich himself or damage others. That's not to say that there aren't dangerous and destructive criminals out there who use social engineering to cause real harm. In fact, that's exactly why Kevin wrote this bookto warn you about them.
The Art of Deception shows how vulnerable we all aregovernment, business, and each of us personallyto the intrusions of the social engineer. In this security-conscious era, we spend huge sums on technology to protect our computer networks and data. This book points out how easy it is to trick insiders and circumvent all this technological protection.
Whether you work in business or government, this book provides a powerful road map to help you understand how social engineers work and what you can do to foil them. Using fictionalized stories that are both entertaining and eye-opening, Kevin and coauthor Bill Simon bring to life the techniques of the social engineering underworld. After each story, they offer practical guidelines to help you guard against the breaches and threats they've described.
Technological security leaves major gaps that people like Kevin can help us close. Read this book and you may finally realize that we all need to turn to the Mitnick's among us for guidance.
Steve Wozniak
Preface
Some hackers destroy people's files or entire hard drives; they're called crackers or vandals . Some novice hackers don't bother learning the technology, but simply download hacker tools to break into computer systems; they're called script kiddies. More experienced hackers with programming skills develop hacker programs and post them to the Web and to bulletin board systems. And then there are individuals who have no interest in the technology, but use the computer merely as a tool to aid them in stealing money, goods, or services.
Despite the media-created myth of Kevin Mitnick, I am not a malicious hacker.
But I'm getting ahead of myself.
STARTING OUT
My path was probably set early in life. I was a happy-go-lucky kid, but bored. After my father split when I was three, my mother worked as a waitress to support us. To see me thenan only child being raised by a mother who put in long, harried days on a sometimes-erratic schedule would have been to see a youngster on his own almost all his waking hours. I was my own babysitter.
Growing up in a San Fernando Valley community gave me the whole of Los Angeles to explore, and by the age of twelve I had discovered a way to travel free throughout the whole greater L.A. area. I realized one day while riding the bus that the security of the bus transfer I had purchased relied on the unusual pattern of the paper-punch that the drivers used to mark day, time, and route on the transfer slips. A friendly driver, answering my carefully planted question, told me where to buy that special type of punch.
The transfers are meant to let you change buses and continue a journey to your destination, but I worked out how to use them to travel anywhere I wanted to go for free. Obtaining blank transfers was a walk in the park.
The trash bins at the bus terminals were always filled with only-partly-used books of transfers that the drivers tossed away at the end of their shifts. With a pad of blanks and the punch, I could mark my own transfers and travel anywhere that L.A. buses went. Before long, I had all but memorized the bus schedules of the entire system. (This was an early example of my surprising memory for certain types of information; I can still, today, remember phone numbers, passwords, and other seemingly trivial details as far back as my childhood.)
Font size:
Interval:
Bookmark:
Similar books «The art of deception: controlling the human element of security»
Look at similar books to The art of deception: controlling the human element of security. We have selected literature similar in name and meaning in the hope of providing readers with more options to find new, interesting, not yet read works.
Discussion, reviews of the book The art of deception: controlling the human element of security and just readers' own opinions. Leave your comments, write what you think about the work, its meaning or the main characters. Specify what exactly you liked and what you didn't like, and why you think so.