Smith - Tor and the Dark Net · Remain Anonymous Online and Evade NSA Spying
Here you can read online Smith - Tor and the Dark Net · Remain Anonymous Online and Evade NSA Spying full text of the book (entire story) in english for free. Download pdf and epub, get meaning, cover and reviews about this ebook. year: 2016, publisher: Pinnacle Publishers, LLC, genre: Romance novel. Description of the work, (preface) as well as reviews are available. Best literature library LitArk.com created for fans of good reading and offers a wide selection of genres:
Romance novel
Science fiction
Adventure
Detective
Science
History
Home and family
Prose
Art
Politics
Computer
Non-fiction
Religion
Business
Children
Humor
Choose a favorite category and find really read worthwhile books. Enjoy immersion in the world of imagination, feel the emotions of the characters or learn something new for yourself, make an fascinating discovery.

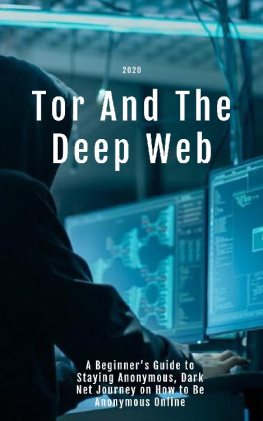
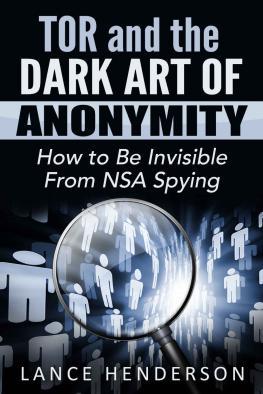
- Book:Tor and the Dark Net · Remain Anonymous Online and Evade NSA Spying
- Author:
- Publisher:Pinnacle Publishers, LLC
- Genre:
- Year:2016
- Rating:4 / 5
- Favourites:Add to favourites
- Your mark:
- 80
- 1
- 2
- 3
- 4
- 5
Tor and the Dark Net · Remain Anonymous Online and Evade NSA Spying: summary, description and annotation
We offer to read an annotation, description, summary or preface (depends on what the author of the book "Tor and the Dark Net · Remain Anonymous Online and Evade NSA Spying" wrote himself). If you haven't found the necessary information about the book — write in the comments, we will try to find it.
Smith: author's other books
Who wrote Tor and the Dark Net · Remain Anonymous Online and Evade NSA Spying? Find out the surname, the name of the author of the book and a list of all author's works by series.
Tor and the Dark Net · Remain Anonymous Online and Evade NSA Spying — read online for free the complete book (whole text) full work
Below is the text of the book, divided by pages. System saving the place of the last page read, allows you to conveniently read the book "Tor and the Dark Net · Remain Anonymous Online and Evade NSA Spying" online for free, without having to search again every time where you left off. Put a bookmark, and you can go to the page where you finished reading at any time.
Font size:
Interval:
Bookmark:
Tor and The Dark Net
Remain Anonymous and Evade NSA Spying
James Smith
Copyrigh t 2016 Pinnacle Publishers
Contents
I want to thank you and congratulate you for downloading the book, Tor and The Dark Net Remain Anonymous and Evade NSA Spying.
Internet privacy is a thing of the past. In todays day and age if you are using a computer or device that is connected to the internet you do not have any privacy. It is an unfortunate, but definite fact. For some this may not matter at all as they dont care who has access to their files, data, browsing habits, or wherabouts. However, for others this can pose a significant problem. The NSA, the FBI, and even simple sophisticated hackers have the ability to track anything and everything you are doing. The good news is there are methods and tactics you can use to prevent this from happening. Inside this book you will find step by step instructions and techniques that can and will make you completely anonymous on the internet. If used correctly not even the NSA will be able to track you down. Everyones situation and needed security levels can be different so this book breaks down all the different options that are available to you and defines exactly what each one does and how secure it can be so that you can choose what will work for you.
It is my hope that this book is able to inform you of all your options to remain anonymous. Thanks again for downloading your copy!
First and foremost, to protect yourself while browsing the internet you should be using Tor which stands for The Onion Router. Tor will provide you with a degree of anonymity by using an 128-bit AES (Advanced Encryption Standard). There has been some debate as to whether or not the NSA can crack this code, and the answer is likely yes. This is why, you should never send anything over Tor that you arent comfortable sharing with the entire world unless you are using some sort of PGP encryption which we will talk about later.
Communication from your computer, to the internet relies on an entry node which basically enters your computer into the Tor network. This entry node communicates with your computer; this entry node knows your IP address. The entry node then passes your encrypted request onto the relay node. The relay node communicates with the entry node and the exit node but does not know your computers IP address. The exit node, is where your request is decrypted and sent to the internet. The exit node does not know your computers IP, only the IP of the relay node. Using this model of 3 nodes it makes it harder, but not impossible to correlate your request to your original IP address.
The problem comes obviously when you are entering plain text into TOR because anybody can set up an exit node. The FBI can set up an exit node, the NSA, or any other foreign government, or any malicious person who may want to steal your information. You should not be entering any sensitive data into any websites, especially when accessing them over TOR. If any of the nodes in the chain are compromised, and some likely are, and the people in charge of those compromised nodes have the computing power to decrypt your request, then you better hope it wasnt anything sensitive.
So what can we do to fix this? Well, luckily we are now having more and more servers that are offering something called Hidden services. You can easily recognize these services by the addres s .onio n . These services offer whats called end-to-end encryption. What this does is take the power out of the compromised exit nodes and put them back in your hands. The web server of the hidden service now becomes your exit node, which means the website you are visiting is the one decrypting your message, not some random exit node ran by a potential attacker. Remember, the exit node has the key to decrypt your request. The exit node can see what you are sending in clear text once they decrypt it. So if you are entering your name and address into a field, the exit node has your information. If you are putting a credit card, a bank account, your real name, even your login information, then you are compromising your identity.
Another step you can take, is to only visit websites that use something called HTTP Secure. You can tell if the website you are visiting is using HTTP Secure by the prefix at the beginning of the address. If you see https:// then your website is using HTTP Secure. What this does is encrypts your requests so that only the server can decrypt them, and not somebody eavesdropping on your communication such as a compromised Tor exit node. This is another form of end-to-end encryption. If somebody were to intercept your request over HTTP Secure, they would see encrypted data and would have to work to decrypt it.
Another reason you want to use HTTPS whenever possible, is that malicious Tor nodes can damage or alter the contents passing through them in an insecure fashion and inject malware into the connection. This is particularly easier when you are sending requests in plain text, but HTTPS reduces this possibility. You must be made aware however, that HTTPS can also be currently cracked depending on the level of the key used to encrypt it. When you visit a website using HTTPS, you are encrypting your request using their public key and they are decrypting it using their private key. This is how cryptography works. A public key is provided to those who want to send an encrypted message and the only one who can decrypt is the one with the private key.
Unfortunately, many websites today are still using private keys that are only 1,024 bits long which in todays world are no longer enough. So you need to make sure you find out which level of encryption the website you are visiting uses, to make sure they are using at a minimum 2,048, if not 4,096 bits. Even doing all of this unfortunately is not enough, because we have another problem. What happens if the web server itself has become compromised? Maybe your TOR nodes are clean, maybe you have used HTTPS for all your requests, but the web server itself of the website you are visiting has been compromised. Well then all your requests are again, as good as plain text.
So keep in mind that if you are a user of the Deep Web, or any other form of activism, you never want to enter any identifying details about yourself online. Make it so that even if the NSA intercepted and decrypted, or compromised the website you are accessing that the only information they have against you is your username and password. How safe is that username and password? Does your password contain any identifying information? Is it the same password that you use for your personal email? Does it contain a name of somebody you know personally? Always keep all of these factors in mind.
Another step you must take, especially when communicating with other users on sites in the Deep Web is using PGP encryption. This is not always possible, such as in cases when you are logging into a website, filling out a form, logging into an email, etc.. Consider any type of information you enter into a website using plain text possibly compromised. Never put anything sensitive in any type of plain text format online. PGP comes into play because it uses a very strong method of encryption called cryptography. PGP stands for Pretty Good Privacy , and it is used for encrypting, decrypting and signing texts, e-mails, files, directories, and whole disk partitions and to increase the security of e-mail communications.
For the more technical users, it uses a serial combination of hashing, data compression, symmetric-key cryptography, and finally public-key cryptography. For the less technical users, the process of encrypting messages using PGP is as follows. You create a private key and a public key. The public key is the key you give out to people you want to send you encrypted messages. Your private key, is kept privately by you. This private key is the only key that can unlock messages that were previously locked with your public key.
Font size:
Interval:
Bookmark:
Similar books «Tor and the Dark Net · Remain Anonymous Online and Evade NSA Spying»
Look at similar books to Tor and the Dark Net · Remain Anonymous Online and Evade NSA Spying. We have selected literature similar in name and meaning in the hope of providing readers with more options to find new, interesting, not yet read works.
Discussion, reviews of the book Tor and the Dark Net · Remain Anonymous Online and Evade NSA Spying and just readers' own opinions. Leave your comments, write what you think about the work, its meaning or the main characters. Specify what exactly you liked and what you didn't like, and why you think so.