Table of Contents
List of Tables
- Introduction
- Chapter 5
List of Illustrations
- Chapter 1
- Chapter 3
- Chapter 4
- Chapter 5
- Chapter 6
- Chapter 7
- Chapter 8
- Chapter 9
- Chapter 10
- Chapter 11
Guide
Pages
(ISC)2
SSCP Systems Security Certified Practitioner
Official Study Guide
Third Edition
Michael S. Wills, SSCP, CISSP, CAMS

Copyright 2022 by John Wiley & Sons, Inc. All rights reserved.
Published by John Wiley & Sons, Inc., Hoboken, New Jersey.
Published simultaneously in Canada.
978-1-119-85498-2
978-1-119-85500-2 (ebk.)
978-1-119-85499-9 (ebk.)
No part of this publication may be reproduced, stored in a retrieval system, or transmitted in any form or by any means, electronic, mechanical, photocopying, recording, scanning, or otherwise, except as permitted under Section 107 or 108 of the 1976 United States Copyright Act, without either the prior written permission of the Publisher, or authorization through payment of the appropriate per-copy fee to the Copyright Clearance Center, Inc., 222 Rosewood Drive, Danvers, MA 01923, (978) 750-8400, fax (978) 750-4470, or on the web at www.copyright.com. Requests to the Publisher for permission should be addressed to the Permissions Department, John Wiley & Sons, Inc., 111 River Street, Hoboken, NJ 07030, (201) 748-6011, fax (201) 748-6008, or online at http://www.wiley.com/go/permission.
Limit of Liability/Disclaimer of Warranty: The publisher and the author make no representations or warranties with respect to the accuracy or completeness of the contents of this work and specifically disclaim all warranties, including without limitation warranties of fitness for a particular purpose. No warranty may be created or extended by sales or promotional materials. The advice and strategies contained herein may not be suitable for every situation. This work is sold with the understanding that the publisher is not engaged in rendering legal, accounting, or other professional services. If professional assistance is required, the services of a competent professional person should be sought. Neither the publisher nor the author shall be liable for damages arising herefrom. The fact that an organization or Website is referred to in this work as a citation and/or a potential source of further information does not mean that the author or the publisher endorses the information the organization or Website may provide or recommendations it may make. Further, readers should be aware the Internet Websites listed in this work may have changed or disappeared between when this work was written and when it is read.
For general information on our other products and services or for technical support, please contact our Customer Care Department within the United States at (800) 762-2974, outside the United States at (317) 572-3993 or fax (317) 572-4002.
Wiley also publishes its books in a variety of electronic formats. Some content that appears in print may not be available in electronic formats. For more information about Wiley products, visit our web site at www.wiley.com.
Library of Congress Control Number: 2021948848
Trademarks: WILEY, the Wiley logo, Sybex and the Sybex logo are trademarks or registered trademarks of John Wiley & Sons, Inc. and/or its affiliates, in the United States and other countries, and may not be used without written permission. (ISC)2 and SSCP are trademarks or registered trademarks of International Information Systems Security Certification Consortium, Inc. All other trademarks are the property of their respective owners. John Wiley & Sons, Inc. is not associated with any product or vendor mentioned in this book.
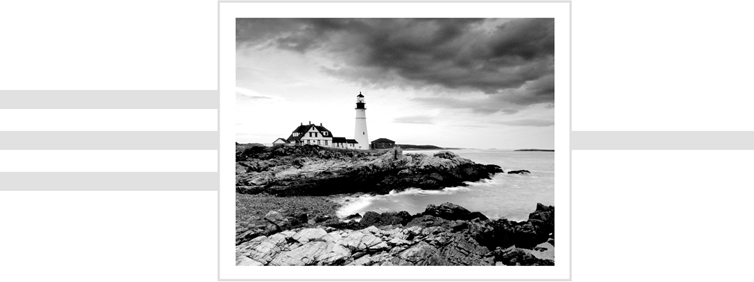
Cover image: Jeremy Woodhouse/Getty Images
Cover design: Wiley
Acknowledgments
This book owes a great deal to the many teachers, co-workers, teammates, and friends who've worked so hard for so long to teach me what I know about information security and insecurity and about risk management and mismanagement. Where this book works well in conveying that body of knowledge, skills, and attitudes to you is a testament to their generosity in sharing their insights with me. (And where it fails to work well, or doesn't work at all, it's my own darned fault.) In particular I'd like to thank the team at (ISC)2 with whom I worked these past 18 months on updates to and then complete revisions of their SSCP and CISSP courses to meet 2021's newly updated exam outlines and content expectations. Countless hours on Zoom and Webex with Graham Thornburrow-Dobson, John Warsinske, Maytal Brooks-Kempler, Laural Hargadon, and Fabio Cerullo sharpened my thinking and focused my writing more toward the operational aspects of cybersecurity and less on the theoretical. A special thank-you too goes out to Kaitlyn Langenbacher, the project owner for these updates at (ISC)2, and to all of the editors and proofreaders working with her. Throughout all of that, the support, questions, and co-creativity they brought made that work a truly joint, collaborative one; their work and care color and shape this revision of this Study Guide as well. I would also like to acknowledge my faculty teammates here at Embry-Riddle Aeronautical University for sharing their frank and candid views throughout many conversations on making this body of knowledge accessible and engaging in the classroom. The ideas and experiences of Drs. Aaron Glassman and Jason Clark have profoundly affected my approach to what you see before you here in this book.
The combined team at Wiley/Sybex and at (ISC)2 worked tirelessly to focus, strengthen, and clarify what I wanted to say here in this book and how I said it, all while keeping my voice and my teaching ideas authentic and on point. My thanks go out to the editorial team at Wiley/Sybex: Jim Minatel, Tracy Brown, Pete Gaughan, Nancy Carrasco, Barath Kumar Rajasekaran, Kim Wimpsett, and their technical reviewer Graham Thornburrow-Dobson, as well as to Tara Zeiler and Fabio Cerullo, our reviewers at (ISC)2. Johnna VanHoose Dinse, Wiley's indexer, has also made the art of finding what you want in this book when you need it more of a science (and I've always had a soft spot for a great index!). Where this book works well for you, it works because of the efforts of all of those people to make this book the best it can be. What errors, omissions, misspeaks, and confusions that remain are mine, not theirs.
Finally, I wish to thank my wife Nancy. She saved my life and brought me peace. Her strength inspired me to say yes the first time when Jim called me about doing this book the first time, and her patience has kept both of us healthy and happy throughout everything. Even these updates.
About the Author
Michael S. Wills, CAMS, CISSP, SSCP, is Assistant Professor of Applied and Innovative Information Technologies at the College of Business, Embry-Riddle Aeronautical University Worldwide, where he continues his graduate and undergraduate teaching and research in cybersecurity and information assurance.