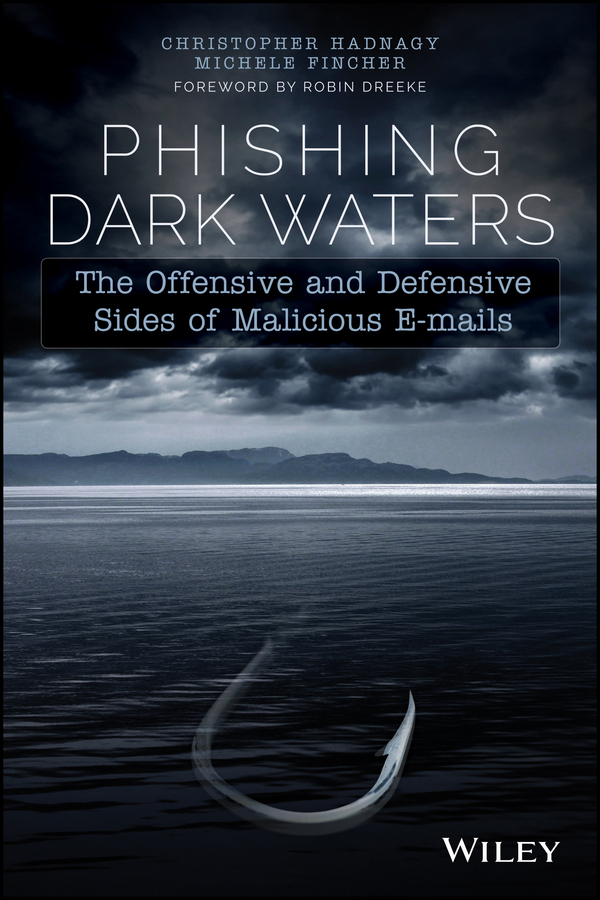
Phishing Dark Waters: The Offensive and Defensive Sides of Malicious E-mails
Published by
John Wiley & Sons, Inc.
10475 Crosspoint Boulevard
Indianapolis, IN 46256
www.wiley.com
Copyright 2015 by John Wiley & Sons, Inc., Indianapolis, Indiana
Published simultaneously in Canada
ISBN: 978-1-118-95847-6
ISBN: 978-1-118-95849-0 (ebk)
ISBN: 978-1-118-95848-3 (ebk)
No part of this publication may be reproduced, stored in a retrieval system or transmitted in any form or by any means, electronic, mechanical, photocopying, recording, scanning or otherwise, except as permitted under Sections 107 or 108 of the 1976 United States Copyright Act, without either the prior written permission of the Publisher, or authorization through payment of the appropriate per-copy fee to the Copyright Clearance Center, 222 Rosewood Drive, Danvers, MA 01923, (978) 750-8400, fax (978) 646-8600. Requests to the Publisher for permission should be addressed to the Permissions Department, John Wiley & Sons, Inc., 111 River Street, Hoboken, NJ 07030, (201) 748-6011, fax (201) 748-6008, or online at http://www.wiley.com/go/permissions.
Limit of Liability/Disclaimer of Warranty: The publisher and the author make no representations or warranties with respect to the accuracy or completeness of the contents of this work and specifically disclaim all warranties, including without limitation warranties of fitness for a particular purpose. No warranty may be created or extended by sales or promotional materials.
The advice and strategies contained herein may not be suitable for every situation. This work is sold with the understanding that the publisher is not engaged in rendering legal, accounting, or other professional services. If professional assistance is required, the services of a competent professional person should be sought. Neither the publisher nor the author shall be liable for damages arising herefrom. The fact that an organization or Web site is referred to in this work as a citation and/or a potential source of further information does not mean that the author or the publisher endorses the information the organization or Web site may provide or recommendations it may make.
Further, readers should be aware that Internet Web sites listed in this work may have changed or disappeared between when this work was written and when it is read.
For general information on our other products and services please contact our Customer Care
Department within the United States at (877) 762-2974, outside the United States at (317) 572-3993 or fax (317) 572-4002.
Wiley publishes in a variety of print and electronic formats and by print-on-demand. Some material included with standard print versions of this book may not be included in e-books or in print- ondemand.
If this book refers to media such as a CD or DVD that is not included in the version you purchased, you may download this material at http://booksupport.wiley.com. For more information about Wiley products, visit www.wiley.com.
Library of Congress Control Number: 2015933609
Trademarks: Wiley and the Wiley logo are trademarks or registered trademarks of John Wiley & Sons,
Inc. and/or its affiliates, in the United States and other countries, and may not be used without written permission. All other trademarks are the property of their respective owners. Wiley Publishing, Inc., is not associated with any product or vendor mentioned in this book.
I dedicate this book to a few people who made it possible. My amazing wife, Areesa, you are one of the most patient, kind, and wise people I have ever met. I hold on to the dream of an eternal future.
Michele, thankfully Ping made that referral a few years ago. Without you this is not possible.
Dave, as I write these words, I can't believe how far we have come. Thank you for your support.
Christopher Hadnagy
This is for my husband, the most beautiful soul in the universe and ruler of all my domains.
And to Chris; thank you for giving me a job and believing in me.
Michele Fincher
About the Authors
Christopher Hadnagy is the founder and CEO of Social-Engineer, Inc. Chris possesses more than 16 years' experience as a practitioner and researcher in the security field. His efforts in training, education, and awareness have helped to expose social engineering as the top threat to the security of organizations today.
Chris established the world's first social-engineering framework at www.social-engineer.org, providing an invaluable repository of information for security professionals and enthusiasts. That site grew into a dynamic web resource, including a podcast and newsletter, which have become staples in the security industry and are referenced by large organizations around the world. Chris also created the first hands-on social-engineering training course and certification, Advanced Practical Social Engineering, which is attended by law enforcement, military, and private sector professionals.
A sought-after writer and speaker, Chris has spoken and trained at events such as RSA, Black Hat, and various presentations for corporate and government clients. Chris is also the best-selling author of two books: Social Engineering: The Art of Human Hacking (Wiley, 2010) and Unmasking the Social Engineer: The Human Element of Security (Wiley, 2014).
Chris specializes in understanding how malicious attackers exploit human communication and trust to obtain access to information and resources through manipulation and deceit. His goal is to secure companies by educating them on the methods used by attackers, identifying vulnerabilities, and mitigating issues through appropriate levels of awareness and security.
Chris is a certified Expert Level graduate of Dr. Paul Ekman's Micro Expressions courses, having made the study of nonverbal behaviors one of his specialties. In addition, he holds certifications as an Offensive Security Certified Professional (OSCP) and an Offensive Security Wireless Professional (OSWP).
Michele Fincher is the Chief Influencing Agent of Social-Engineer, Inc. She has more than 20 years' experience as a behavioral scientist, researcher, and information security professional. Michele's diverse background has helped solidify Social-Engineer, Inc.'s place as the premier social-engineering consulting firm.
As a U.S. Air Force officer, Michele's assignments included the USAF Academy, where she was a National Board Certified Counselor and Assistant Professor in the Department of Behavioral Sciences and Leadership. Upon separating from the Air Force, Michele went on to hold positions with a research and software development firm in support of the U.S. Air Force Research Laboratory, as well as with an information security firm, where she conducted National Security Agency appraisals and Certification and Accreditation for federal government information systems.
At Social-Engineer, Inc., Michele is a senior penetration tester with professional expertise in all facets of social-engineering vectors, assessments, and research. A remarkable writer, she is also the talent behind many of the written products of Social-Engineer, Inc., including numerous reports and assessments, blog posts, and the Social-Engineer Newsletter.
Michele is an often-requested trainer and speaker on various technical and behavioral subjects for law enforcement, the intelligence community, and the private sector in venues including the Black Hat Briefings, RSA, Techno Security, and the
Next page