David Kahn - The Codebreakers
Here you can read online David Kahn - The Codebreakers full text of the book (entire story) in english for free. Download pdf and epub, get meaning, cover and reviews about this ebook. year: 1996, publisher: Simon & Schuster, genre: Detective and thriller. Description of the work, (preface) as well as reviews are available. Best literature library LitArk.com created for fans of good reading and offers a wide selection of genres:
Romance novel
Science fiction
Adventure
Detective
Science
History
Home and family
Prose
Art
Politics
Computer
Non-fiction
Religion
Business
Children
Humor
Choose a favorite category and find really read worthwhile books. Enjoy immersion in the world of imagination, feel the emotions of the characters or learn something new for yourself, make an fascinating discovery.

- Book:The Codebreakers
- Author:
- Publisher:Simon & Schuster
- Genre:
- Year:1996
- Rating:3 / 5
- Favourites:Add to favourites
- Your mark:
- 60
- 1
- 2
- 3
- 4
- 5
The Codebreakers: summary, description and annotation
We offer to read an annotation, description, summary or preface (depends on what the author of the book "The Codebreakers" wrote himself). If you haven't found the necessary information about the book — write in the comments, we will try to find it.
The Codebreakers — read online for free the complete book (whole text) full work
Below is the text of the book, divided by pages. System saving the place of the last page read, allows you to conveniently read the book "The Codebreakers" online for free, without having to search again every time where you left off. Put a bookmark, and you can go to the page where you finished reading at any time.
Font size:
Interval:
Bookmark:

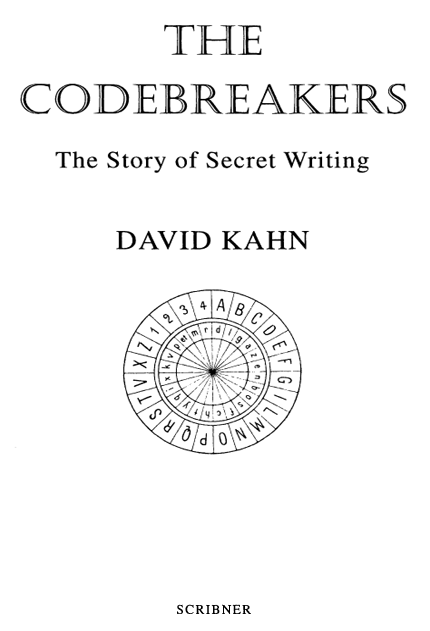

SCRIBNER
1230 Avenue of the Americas
New York, NY 10020
www.SimonandSchuster.com
Copyright 1967, 1996 by David Kahn
All rights reserved, including the right of reproduction in whole or in part in any form.
SCRIBNER and design are trademarks of Macmillan Library Reference USA, Inc. under license by Simon & Schuster, the publisher of this work.
Manufactured in the United States of America
13 15 17 19 20 18 16 14 12
Library of Congress Cataloging-in-Publication Data is available.
ISBN 0-684-83130-9
ISBN: 978-0-684-83130-5
eISBN: 978-1-439-10355-5
To my Parents and my Grandmother
The need to revise this book existed even before it was published on September 27, 1967. I had written what I hoped would be the definitive history of the subject. I did not know at the time of such great matters as the Polish-British-American mastery of the German Enigma cipher machine, which had such great effects on World War II, or of such lesser ones as the tactical value of German front-line telephone taps. Nor did Ior anyoneknow of things that had not yet been invented, such as public-key cryptography. The first glimmering that the world of cryptology would not stand still for me came four months after publication, when North Korea seized the U.S. electronic reconnaissance ship Pueblo in January 1968. It marked the first of a series of events that showed the need for revision. I had, indeed, made some minor corrections in printings three through seven, but then I concentrated on other projects.
There followed, however, the Ultra disclosures, the creation of public-key cryptography, and the enormous growth in computer communications, including particularly the appearance of the Internet, where cryptography affords the best means for privacy. At about the same time, the absorption of Macmillan, the original publisher, by Simon & Schuster brought a young, energetic editor named Scott Moyers to handle The Codebreakers. He saw that I could fulfill my obligation to cryptology and at the same time help the book sell better by incorporating the new material as a single chapter. This made sense, and that is what Ive done.
I have sought to cover the major events, both external and internal, that have affected cryptology in the past quarter century. It is amazing how much these have changed the field. Fortunately for me, while they have added information, they do not change the past, so the first edition remains valid. I hope that this new edition will prove as usefuland perhaps as pleasurableto readers as the previous one.
D AVID K AHN
Great Neck, New York
May 1996
CODEBREAKING is the most important form of secret intelligence in the world today. It produces much more and much more trustworthy information than spies, and this intelligence exerts great influence upon the policies of governments. Yet it has never had a chronicler.
It badly needs one. It has been estimated that cryptanalysis saved a year of war in the Pacific, yet the histories give it but passing mention. Churchills great history of World War II has been cleaned of every single reference to Allied communications intelligence except one (and that based on the American Pearl Harbor investigation), although Britain thought it vital enough to assign 30,000 people to the work. The intelligence history of World War II has never been written. All this gives a distorted view of why things happened. Furthermore, cryptology itself can benefit, like other spheres of human endeavor, from knowing its major trends, its great men, its errors made and lessons learned.
I have tried in this book to write a serious history of cryptology. It is primarily a report to the public on the important role that cryptology has played, but it may also orient cryptology with regard to its past and alert historians to the sub rosa influence of cryptanalysis. The book seeks to cover the entire history of cryptology. My goal has been twofold: to narrate the development of the various methods of making and breaking codes and ciphers, and to tell how these methods have affected men.
When I began this book, I, like other well-informed amateurs, knew about all that had been published on the history of cryptology in books on the subject. How little we really knew! Neither we nor any professionals realized that many valuable articles lurked in scholarly journals, or had induced any cryptanalysts to tell their stories for publication, or had tapped the vast treasuries of documentary material, or had tried to take a long view and ask some questions that now appear basic. I believe it to be true that, from the point of view of the material previously published in books on cryptology, what is new in this book is 85 to 90 per cent.
Yet it is not exhaustive. A foolish secrecy still clothes much of World War II cryptologythough I believe the outlines of the achievements are knownand to tell just that story in full would require a book the size of this. Even in, say, the 18th century, the unexplored manuscript material is very great.
Nor is this a textbook. I have explained at length only two basic methods of solution, though I have sketched many others. For some readers even this will be too much; them I advise to skip this material. They will not have a full understanding of what is going on, but that will not cripple their comprehension of the stories. For readers who want more detail on these methods, I recommend Helen F. Gainess Elementary Cryptanalysis, partly because it is a competent work, partly because it is the only work of its kind in English now easily available (in a paperback reprint, entitled Cryptanalysis). In French, there is Luigi Saccos outstanding Manuel de cryptographie (the Italian original is out of print). Nearly all the other books in print are juveniles. Readers interested in cryptanalysis may also join the American Cryptogram Association, which publishes a magazine with articles on how to solve ciphers and with cryptograms for solution.
In my writing, I have tried to adhere to two principles. One was to use primary sources as much as possible. Often it could not be done any other way, since nothing had been published on a particular matter. The other principle was to try to make certain that I did not give cryptology sole and total credit for winning a battle or making possible a diplomatic coup or whatever happened if, as was usual, other factors played a role. Narratives which make it appear as if every event in history turned upon the subject under discussion are not history but journalism. They are especially prevalent in spy stories, and cryptology is not immune. The only other book-length attempt to survey the history of cryptology, the late Fletcher Pratts Secret and Urgent, published in 1939, suffers from a severe case of this special pleading. Pratt writes thrillinglyperhaps for that very reasonbut his failure to consider the other factors, together with his errors and omissions, his false generalizations based on no evidence, and his unfortunate predilection for inventing facts vitiate his work as any kind of a history. (Finding this out was disillusioning, for it was this book, borrowed from the Great Neck Library, that interested me in cryptology.) I think that although trying to balance the story with the other factors may detract a little from the immediate thrill, it charges it with authenticity and hence makes for long-lasting interest: for this is how things really happened.
Next pageFont size:
Interval:
Bookmark:
Similar books «The Codebreakers»
Look at similar books to The Codebreakers. We have selected literature similar in name and meaning in the hope of providing readers with more options to find new, interesting, not yet read works.
Discussion, reviews of the book The Codebreakers and just readers' own opinions. Leave your comments, write what you think about the work, its meaning or the main characters. Specify what exactly you liked and what you didn't like, and why you think so.